This research report written by Louis Melançon for Serene-risc in August 2020, provides a cybersecurity overview of the Canadian health sector. It looks at the latest statistics concerning the cybersecurity practices of Canadian health businesses. This report also presents each of the five major cyber threats to healthcare and examines the recommended security safeguards and measures. Finally, it covers …
Les problématiques reliés à la cybersécurité touchent tout le monde. En effet, peu importe notre âge ou l’endroit où nous vivons, en 2020, nous utilisons les technologies quotidiennement. Au travail, à la maison, à l’école ou pour communiquer avec autrui, nous avons toujours soit un téléphone cellulaire, un ordinateur portable ou une tablette près de …
Here are the latest scientific publications our co-investigators: Books C Boyd, A Mathuria, D. Stebila: Protocols for Authentication and Key Establishment, Second Edition, Information Security and Cryptography. Springer, 2019. In press. Blayne Haggart, Kathryn Henne, N. Tusikov: Information, Technology and Control in a Changing WorldUnderstanding Power Structures in the 21st Century Book chapters Barry Cartwright, George RS Weir, R. …
Our co-investigator Holly-Ann Garnett published a new article on evaluating online registration. The article evaluates online voter registration, using the case of Elections Canada’s introduction of an online voter registration service in advance of the 2015 Canadian general election. It asks two major questions: (1) What sociodemographic and attitudinal characteristics can predict online registration usage? …
The workplace is a radically different environment since Information Systems (IS) became one of the strongest enablers for its processes. But IS can be misused. Security issues in IS are becoming more prevalent than ever before. In addition to the significant damage of these acts, the stakeholders deemed accountable for these events have faced severe …
Information Security Policy Compliance: An Empirical Study of Rationality-Based Beliefs and Information Security Awareness Burcu Bulgurcu and researchers from the Saunders School of Business at the University of British Colombia looked into the problem of employees not complying with security policy. Security policy is (generally) put in place to protect the company from attacks directed …
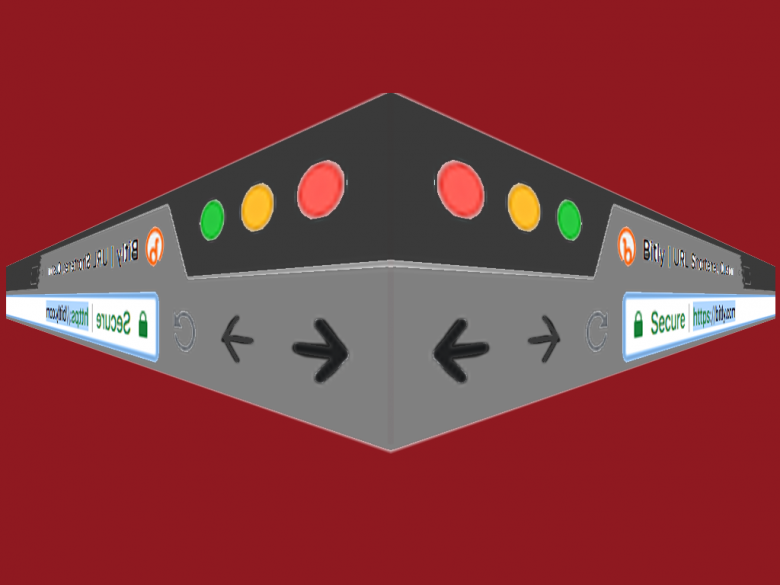
URL shortening services provide a short link in place of a long URL. Attackers sometimes use these services to mask the URL of a malicious destination, making it harder for a person to detect a link that they shouldn’t click on. A group from the university of Ottawa and IBM collected 300 thousand malicious …
Crime statistics are a curious thing. Data available from police and the courts provide well-defined set of numbers but are limited by the amount of crime reported to and processed by the police and other over-burdened institutions. If we are to understand where we are lacking, we need to assess the gap between the actual …
Cormac Herley presents work done with Paul van Oorshot on some historic ideas that might help us work towards a common science for information security. This is something that we all need in order to progress the field. “Claims that uniques aspects of security exempt it from a scientific approach are unhelpful.” There has been …
Criminals documenting themselves doing something illegal seems counterproductive. Creating a video that could prove their guilt seems bizarre. Even though it is illogical, it still happens. Sveinung Sandberg and Thomas Ugelvik looked into this phenomenon. They analyzed 51 Norwegian higher court decisions involving the use of a camera as an integrated part of an offence. …