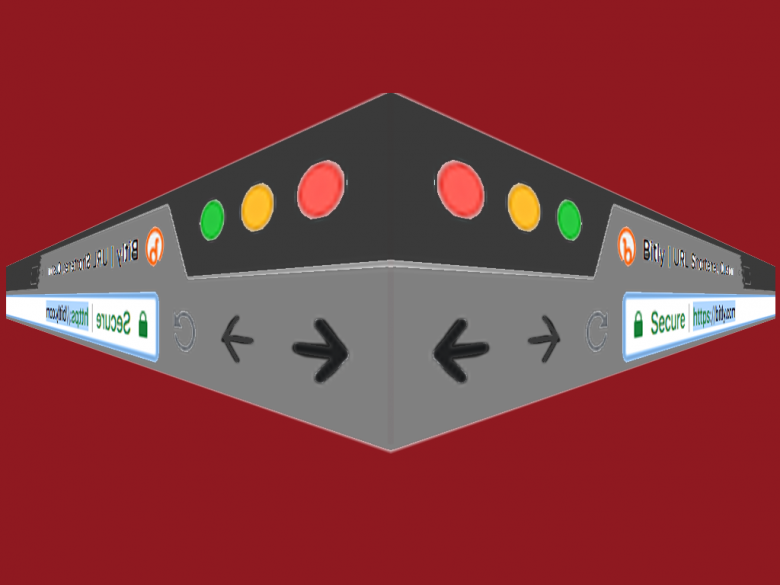
URL shortening services provide a short link in place of a long URL. Attackers sometimes use these services to mask the URL of a malicious destination, making it harder for a person to detect a link that they shouldn’t click on. A group from the university of Ottawa and IBM collected 300 thousand malicious URLS and identified 7,000 shortened links that use the bitty service.
They found that phishing URLs receive more click through traffic. 40% of mal-ware URLs receive more than 27 clicks compared to 80% of phishing URLs. There is a general conception that malware and phishing attacks are changed so rapidly that they are difficult to combat, the proverbial game of whack-a-mole. However they found that 50% of malware URLs are active for several years and 50% of phishing URLs are active for more than 3 months. This difference in time scale seemed to match with how long the attacks were effective. For phishing they found the highest click activity to be 4 hours before the link was reported. The links were still being clicked up to 6 months later.
With malware they found the highest click activity to be 4 days before the report date. Interestingly they also found “several other peaks before and after, indicating that our sources are not catching active malware URLs, and also indicating that malware URLs are successfully resurfacing”—p.p. 12.
I found the results about the difference in time scale to be particularly interesting. Are we better at responding to phishing than malware ? Could it be that the greater investment in deploying malware results in more effort from offenders in extracting clicks ? This research certainly points to some interesting phenomena, and adds more weight to the argument that we aren’t as good at whacking moles as we assumed we were.
S. Le Page, G. V. Jourdan, G. V. Bochmann, J. Flood and I. V. Onut, “Using URL shorteners to compare phishing and malware attacks,” 2018 APWG Symposium on Electronic Crime Research (eCrime), San Diego, CA, 2018, pp. 1-13.
doi: 10.1109/ECRIME.2018.8376215
URL: http://ieeexplore.ieee.org/stamp/stamp.jsp?tp=&arnumber=8376215&isnumber=8376205