According to Schoffstall and Cohen (2011), cyber aggression is defined as behaviour committed with the intent to harm an individual, using a computer, cell phone or other electronic devices. In addition, the authors nuanced that the behaviour must be perceived as aversive by the victim. Cyber victimization is like cyber aggression but includes in its …
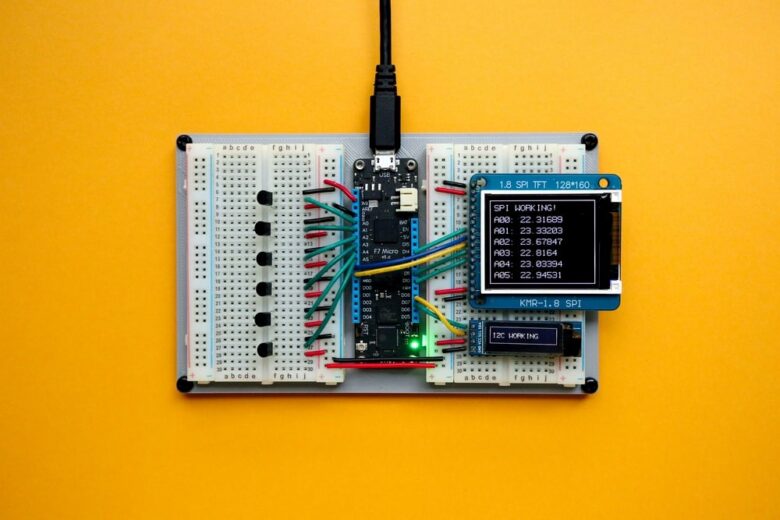
The Internet of Things (IoT), cloud computing technology, and health technologies are essential tools in 2021 to ensure the well-being and running of individuals and organizations’ activities in our society. However, considering the importance of connected objects and the irreplaceable place they occupy, it is vital to ensure that they are well protected against malware …
Considering that cybersecurity and cybercrime are often used in the cyber world, should they be related? Cybercrime represents the study of all “cyber” crimes. When mentioned, it is generally referring to the field of study of traditional offences committed on the Internet, crimes that have been created and which take shape strictly on the Internet …
Cybersecurity bicycle attacks consist of data leaks caused by a security weakness related to password length through encrypted traffic. This terminology, coined by Vranken (2016), was created following the observation by this researcher that SSL (unpadded) traffic can allow the disclosure of information about the length of passwords. He named this phenomenon the “bicycle attack,” …
Numerous studies demonstrate the significant impact of human behaviour on the cybersecurity of a company or organization. The human aspect behind protecting security breaches cannot be overlooked. Humans often act as a firewall on the first line of defence in the computer network cybersecurity experts try to preserve, and hackers try to destroy. Therefore, training …
Mobile devices have become a necessity in 2021. Both in personal and professional life, humans cannot live without them. Smart cell phones are often connected to work, and employees have access to valuable data even when away from the workplace. As a result, significant data breaches continue to increase and threaten the security of customer’s …
Fraud has been an extremely prevalent crime since the evolution of the Internet. The modalities in which it takes shape, mainly on the World Wide Web (WWW), make its prevention and retribution highly complex to police agencies. These law enforcement agencies do not appear to be adequate, and the traditional methods put in place seem …
Unsurprisingly, social networks have dramatically increased in popularity in recent years. The use of sites serving as social network sites (SNS) continues to increase, and most humans would not be able to live without them. For example, the most popular SNS, Facebook, had 69 million active users in 2008. As of 2018, it had 2,600 …
Social conformity is a well-studied phenomenon in psychology, especially in sociopsychology, mainly due to its influence on human behaviour. Indeed, conformity is a social phenomenon that causes individuals to change their behaviours, vision, or opinions to agree with the majority (Asch, 1951). These behaviours are mainly explained by the human tendency to be appreciated by …
The strong growth in computer security incidents forces private companies and government organizations to improve and be aware of hackers’ new tacticss continually. To do this, these organizations must equip themselves with numerous hardware and software at the cutting edge of technology. Despite this, if no one can use them well or know how to …