Like cybercrime, large-scale cyber-attacks are overgrowing and attracting attention from both media and government agencies mainly because these attacks are often linked to threats of cyberterrorism. A misconception is to take for granted that cyberterrorism is precisely the same phenomenon as terrorism and then uses the exact definition for both phenomena. Moreover, even the definition of terrorism changes a lot depending on the studies and the circumstances. The novelty of the cyber phenomenon makes the task even more complicated for researchers to define the problem. To date, the various studies that deal with cyber-terrorism use different definitions that are imprecise and vary according to the needs or circumstances of the study. Taxonomies found in the scientific literature do not distinguish cyberterror actors from other types of cyber actors. This leads studies to include types of acts or perpetrators of different types of cybercrime in the definition.
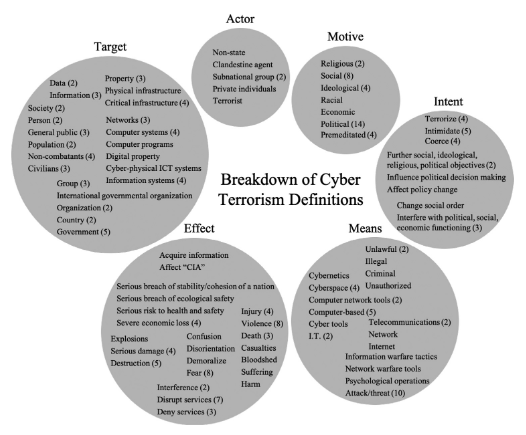
Therefore, this study addresses the different definitions found in scientific articles. The researchers analyzed multiple definitions intending to find a universal definition that consolidates existing ones. To do this, Plotnek and Slay (2021) conducted a literature review of all the articles trying to define the problem. The various studies observed a modified taxonomy of cyberterrorism that brought together all the themes that often came up in definitions (figure 1). The researchers then used this taxonomy from Al Mazari et al. (2018) to establish their taxonomy basis and further research. They then grouped with the different definitions and main themes recurring in the previous taxonomy studies (figure 2).
Figure 1: New cyber terrorism taxonomy, revised from an original taxonomy proposed by Al Mazari & all. (, 2018).
Figure 2: Features inherent to cyber terrorism, as defined in current literature, grouped according to the revised taxonomy in figure 1.
Finally, after the analysis, the researchers provided a taxonomy and a standard definition of cyber terrorism.
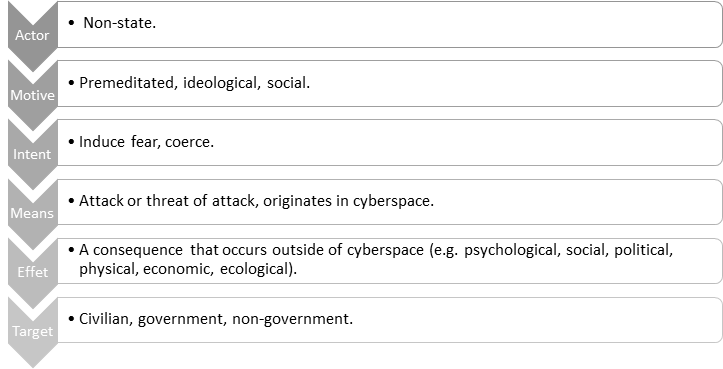
Definition:
“Cyber terrorism is the premeditated attack or threat thereof by non-state actors with the intent to use cyberspace to cause real-world consequences in order to induce fear or coerce civilian, government, or non-government targets in pursuit of social or ideological objectives. Real-world consequences include physical, psychosocial, political, economic, ecological, or otherwise that occur outside of cyberspace.”
This article establishes a clear foundation in the study of cyber terrorism, which seemed to take different forms according to past studies. Being a relatively new topic, studies must focus on the very basics of the phenomenon to better direct subsequent studies.



