Ransomware is a type of malware that has grown in popularity over the past few years. However, its popularity does not come from its social appreciation but more from its significant threat, particularly to Windows users. Ransomware is designed to encrypt or outright block access to data on the victim’s computer. This malware can take all documents, old backups, and databases available on the computer hostage depending on its functions until the computer’s owner pays a ransom. Subsequently, the malicious individuals release the information held hostage. This type of attack targets individuals, but mainly companies or even universities, as seen in the past.
Considering the increase in ransomware cases and their significant damage, researchers Lemmou, Lanet, and Souidi (2020) focused on behaviours and modus operandi of ransomware that caused the most damage to victims in recent years. They mainly focus on crypto-ransomware that surfaced on Windows during the years 2017, 2018, and 2019.
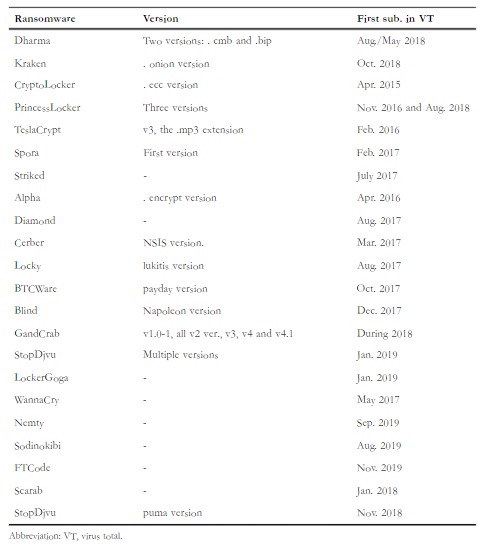
To do this, the researchers analyzed behaviours and modus operandi of ransomware, drawing from a manually collected list of more than 20 families of ransomware. In addition, some behaviours of more than 200 ransomware collected in 2019 have been automatically extracted for analysis. These analyses aimed to highlight the typical behaviours of this malware to identify them better.
After completing their analyzes, the researchers managed to categorize typical ransomware behaviours into three categories:
1. Pre-encryption behaviours are usually performed by the ransomware before the data encryption. These behaviours are self-reproduction, superinfection management, process installation, persistent / evasion mechanisms, network activities, etc.
2. Behaviours during encryption are behaviours monitored during file encryption, such as exploring the file system (to find the documents to be encrypted) and encryption process (reading, writing, deleting, moving, renaming, change of extension, etc.).
3. Post-encryption behaviours are observable behaviours after infection of the computer. They refer to the display of ransom notes (message directed to the computer owners) and the removal of shadow copies of the victim machine.
This article has a critical empirical and practical contribution. Indeed, it makes it possible to demystify the typical behaviours observable in ransomware that has claimed hundreds of thousands of victims worldwide in recent years. This information enriches our knowledge of this type of attack and allows them to be better detected.
To cite: Lemmou, Y., Lanet, J-L., Souidi, M. (2020). A behavioural in-depth analysis of ransomware infection, IET Information Security, 15, 38-58.https://doi.org/10.1049/ise2.12004



