Like a lot of good stories, this one starts with a chance encounter, a quiet conversation and a cold beer*.
Sebastian Feldmann, the author of “Chaos: A Stolen Backdoor Rising Again” who is currently completing his master’s thesis at the Technical University of Darmstadt took the time to speak with me about his recent experience as an intern at a Canadian security firm. How to get a start in the security industry is a question that comes up very often at conferences and on social media. In Sebastian’s case, it seems that the old-fashioned approach of being passionate about the craft, getting out and meeting people was the catalyst.
“The very first time I met Olivier from Gosecure was at Northsec in 2016 and it was totally random that I met him again at Blackhat in London, where he gave a talk about the Linux/Moose malware” related Sebastian, “In London we had some very interesting conversations about GoSecure, their research department and their projects so I applied for an internship at GoSecure and was happy to be accepted.”
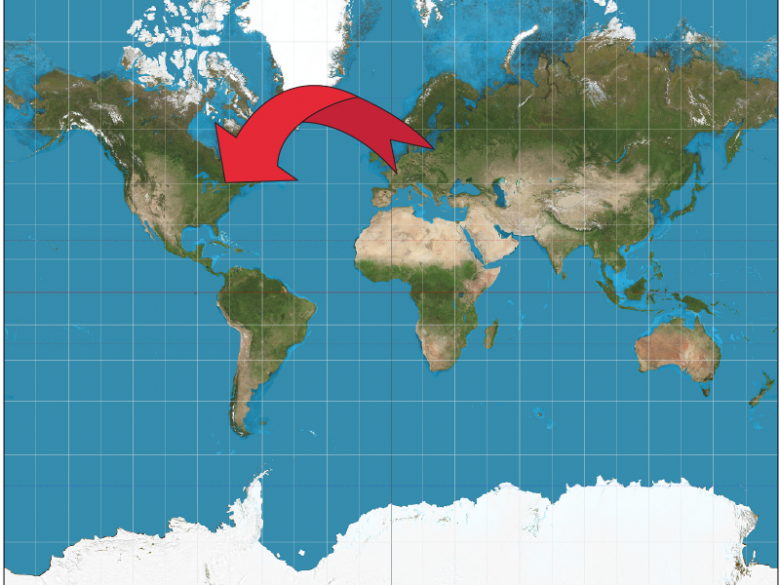
During his internship he undertook a project to find if there was malware targeting FreeBSD. FreeBSD is an open source operating system that, although little known outside of technical circles is an important part of the modern information technology world. A number of large companies such as ‘Netflix’ and ‘Whatsapp’ use it for their servers and it is used as a base for consumer systems; such as the PlayStation 4. FreeBSD is generally considered to be quite secure, but the combination of system scarcity and the potential importance of the services relying on it places it in an interesting space. It is perhaps less lucrative to develop malware for FreeBSD, as there are less systems out there, but there is a smaller community to detect and remedy or patch against malware. This begs the question, is there any malware out there? To answer this question, Sebastian set up custom built honeypots and distributed them around the world to attract attackers and their malware to analyse.
“The results were rather disappointing as almost every attacker left the honeypot after realizing that the server was running FreeBSD. When attackers ‘breached’ the system I was able to see them typing commands in real time which at first was a bit scary to witness, but later also very funny as many attackers seemed not to know how Linux (or especially FreeBSD) works and mistyped and misconfigured their own payloads.”
The outcome of the test was that they didn’t find any malware designed for FreeBSD. That is not to say they didn’t find anything. When they broadened the focus of the project to include malware targeting the more common Linux operating system, there was plenty of insight to be gained. “It was super interesting to see that every five minutes someone attempted to connect [to the computer]”, said Sebastian, “I had thought there would be one or two a day, but actually it was much, much more”
Gathering samples is just part of the work, it is important to understand what the malware is doing to understand the potential impact for someone finding that code on their computer. Malware is found as an executable file, or a file designed to be read and processed by a computer; not by humans. This requires a process of reverse engineering or stepping backwards through the process of software production to find clues about the purpose of the program. This is a difficult task at the best of times and the secretive nature of malware makes it particularly challenging. Malware reverse engineering requires a good understanding of computer science theory and a great practical understanding. A good internship is a great place to take a theoretical understanding and put it into practice. On this particular project Sebastian noted, “The malware sample that I described in the blog-post was rather difficult to reverse as it included a lot of cryptography and integrity checks using shared keys that were negotiated during a custom handshake protocol. It was the very first time for me to reverse a more complicated and real-world malware sample and I had to learn many new things.” Although there was much to learn, the hard hours in the classroom seem to have paid off when the time came for application. “It’s funny” Sebastian chuckled, “here we say that our university is so theoretical that we wouldn’t use most of it in real life, and then the very first malware I found was using everything that I had learnt, so I kind of have to say ‘thank you university’.” Curious about how it was to adapt from university to the work environment at a time when there is such a demand for security services, I asked him about what it is really like working in security research.
“Working in security research is highly dynamic as the techniques are changing rapidly and need to be adapted quite fast. It is a constantly changing environment so you must not be afraid to learn something new or even worse be to satisfied with your knowledge. Of course, it is super satisfying to finally understand a malware sample or to find an elegant solution to a specific problem which makes all the hard work totally worth it.”
If you are running FreeBSD or Linux servers it is work checking out Sebastian’s post (http://gosecure.net/2018/02/14/chaos-stolen-backdoor-rising/), as the backdoor malware may not have been picked up by some automated detection systems. Those interested in Linux malware, attackers behavior on a system and cryptography also wouldn’t waste the few minutes to review the blog.
It is great to see Canadian companies attracting talent from around the world and interesting to learn about not only the great people working on security here, but also how they got into what is often considered a confusing and secretive specialist field. I look forward to seeing what Mr. Feldmann is working on next.
Thank you to Sebastian Feldmann for giving up his time to share his experiences and to GoSecure for helping to make the connection.
* I wasn’t there and did not confirm the presence of beer in this story, so please excuse the ‘artistic licence’, it just seemed natural.