A group from Northwest University, China, and the University of Bath and Lancaster University in the UK have come up with a method for determining android unlock patterns. The method uses video footage captured by a smartphone and an algorithm that can determine likely codes that match the movement of the finger or hand across …
Month: July 2017
Vinay Kaura provides some insight into the impact of the Internet on insurgency in the region of Kashmir. This region has famously been in conflict for more than half a century and has crossed over into the digital realm. The problems are deeply complex and the informatization of the region has created additional layers with …
A keynote address by Erinn Clark, Lead Security Architect, First Look Media/The Intercept More than 80 refereed paper presentations as well as invited talks, a poster session, a doctoral colloquium, a Work-in-Progress session, and Birds-of-a-Feather sessions. Sheraton Vancouver Wall Centre Hotel 1088 Burrard Street Vancouver, BC, V6Z 2R9 Canada https://www.usenix.org/conference/usenixsecurity17
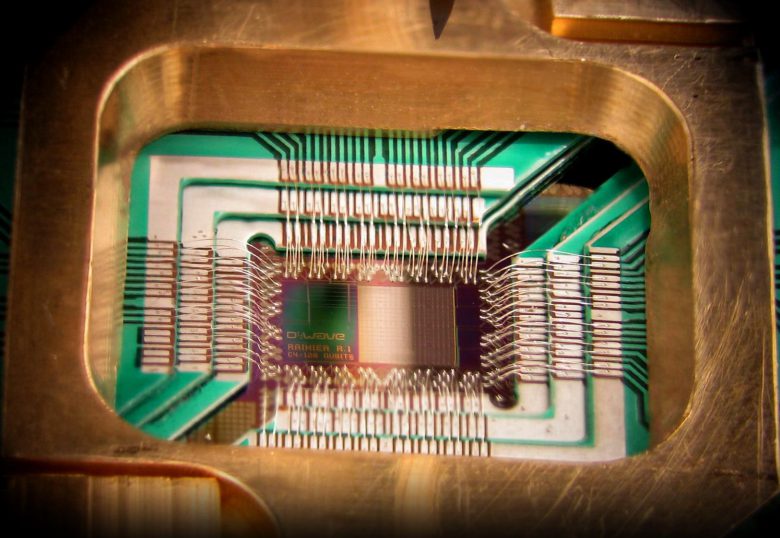
Dr. Michele Mosca reminds us an unfortunate truth as laid bare by Max Planck “A new scientific truth does not triumph by convincing its opponents and making them see the light, but rather because its opponents eventually die, and a new generation grows up that is familiar with it.” Quantum Computing is an area …
Highly secure systems are often ‘Air Gapped’, or removed from any internet connected network to make it more difficult to illegally or maliciously access them. Attacks in recent years have shown that it is possible and perhaps not even particularly complex to have users load malicious software onto an air gapped computer (e.g. with a …
While threats that manifest in cyberspace are a national security imperative, they often manifest at a very local level. Digital connectivity is driving shifts in the policing landscape and new operating models are needed to confront the challenges of crimes enabled by the Internet. As a former Deputy Chief of Police with the Toronto …
Samantha Bates at Simon Fraser University has examined the emotional and mental health effects on survivors of revenge pornography. This form of non-consensual distribution of intimate images occurs after partners exchange intimate photos during a relationship, but when the relationship breaks down, one of the former partners distribute the images to the family, friends, employers …
Terrorism and the Internet is a hot button topic with the dangers posed by online groups being the subject of near constant debate and news headlines. A question that bears closer examination is the effect that the Internet has on would be terrorists. Does content or contact online cause a change in behaviour or does …
Timothy Rich at Western Kentucky University was interested to see if appeals in Advanced Fee Fraud emails for the recipient to trust them were effective at all. To do this he surveyed a large number of advanced fee fraud type emails to develop models of standard email text. These texts were then modified to include …