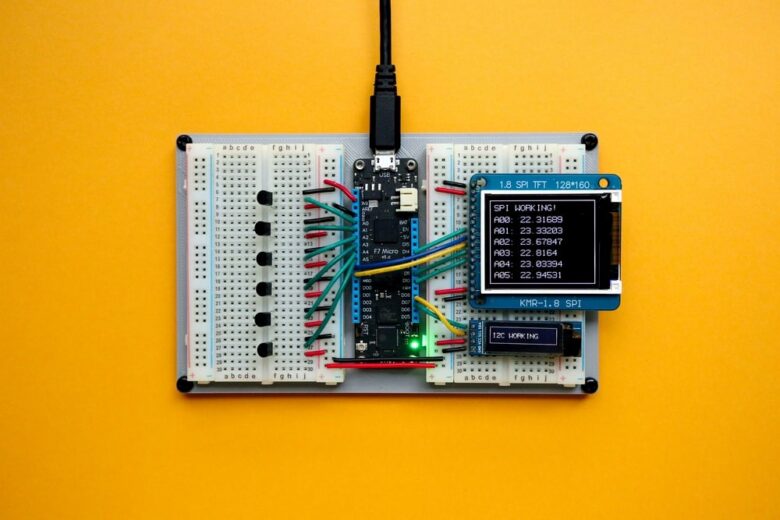
L’internet des objets (IoT) (« Internet of things » en anglais), la technologie par nuagerie informatique et les technologies de santé sont des outils primordiaux en 2021 pour assurer le bien-être et le roulement des activités des individus et des organisations primordiales dans notre société. Considérant l’importance des objets connectés, et la place irremplaçable qu’ils occupent, il …
Considérant que les termes cybersécurité et cybercrime sont souvent utilisés dans le cyberespace, ne devraient-ils pas être reliés? La cybercriminalité représente l’ensemble des crimes « cyber ». Lorsqu’on y fait mention, on fait généralement référence au domaine d’étude des crimes traditionnels qui sont commis sur l’Internet, des crimes qui y sont créés et qui y prennent forme …
Considering that cybersecurity and cybercrime are often used in the cyber world, should they be related? Cybercrime represents the study of all “cyber” crimes. When mentioned, it is generally referring to the field of study of traditional offences committed on the Internet, crimes that have been created and which take shape strictly on the Internet …
Cybersecurity bicycle attacks consist of data leaks caused by a security weakness related to password length through encrypted traffic. This terminology, coined by Vranken (2016), was created following the observation by this researcher that SSL (unpadded) traffic can allow the disclosure of information about the length of passwords. He named this phenomenon the “bicycle attack,” …
Les social-bots sont des robots possédant des fonctions automatisées qui sont créés par des humains afin d’effectuer des tâches précises sur les réseaux sociaux. Ces bots peuvent avoir une utilité légitime, comme faire du marketing pour une compagnie, ou illégitime comme pour faire de la désinformation. Il a aussi été vu par le passé que …
Social bots are robots with automated functions built by humans to perform specific tasks on social media. These bots can have a legitimate use, such as marketing for a company, or illegitimate, such as misinformation. As shown in the past, social bots can play an important role in election campaigns. These have since increased in …
De nombreuses études démontrent l’impact important des comportements humains sur la cybersécurité d’une entreprise ou d’une organisation. L’aspect humain derrière la protection des failles de sécurité ne peut être négligé. Les humains agissent bien souvent comme un pare-feu sur la première ligne de défense du réseau informatique que les experts en cybersécurité tentent de protéger …
Numerous studies demonstrate the significant impact of human behaviour on the cybersecurity of a company or organization. The human aspect behind protecting security breaches cannot be overlooked. Humans often act as a firewall on the first line of defence in the computer network cybersecurity experts try to preserve, and hackers try to destroy. Therefore, training …
Les appareils mobiles sont devenus une nécessité en 2021. Autant dans la vie personnelle que professionnelle, les humains ne peuvent vivre sans eux. Les téléphones cellulaires intelligents sont particulièrement souvent reliés au travail, et les employés ont accès à des données précieuses même à distance du milieu de travail. Conséquemment, les violations de données importantes …
Mobile devices have become a necessity in 2021. Both in personal and professional life, humans cannot live without them. Smart cell phones are often connected to work, and employees have access to valuable data even when away from the workplace. As a result, significant data breaches continue to increase and threaten the security of customer’s …