We all have questions, but who are the people with the answers for Cybersecurity. In this series, we sat down with academics and experts to ask them about how they got started, what they are researching now, their lessons for us, and the future. In this last episode, Holly An Garnett, Assistant Professor of Political …
Month: April 2020
Les fonctionnalités et l’utilisation des téléphones intelligents ont considérablement changé au cours des dernières années. La quantité croissante de données personnelles et privées sur les téléphones intelligents font de ces appareils, une cible populaire pour le vol. Il existe plusieurs études sur la sensibilisation des utilisateurs de téléphones intelligents et leurs préoccupations en matière de …
Smartphone features and usage have changed significantly over the past few years. The increasing amount of personal and private data on those devices makes them a popular target for theft. There have been several studies on smartphone user’s awareness and concerns regarding security. Some studies have revealed that due to a low level of security …
We all have questions, but who are the people with the answers for Cybersecurity. In this series we sat down with academics and experts to ask them about how they got started, what they are researching now, their lessons for us and the future. In this video, Holly An Garnett, Assistant Professor of Political Science …
Les technologies de l’information et de la communication sont des ressources essentielles pour les organisations de nos jours et, comme de grandes quantités d’informations circulent quotidiennement, la protection des informations devient une priorité. Différentes méthodologies d’analyse des risques pour la sécurité de l’information permettent d’étudier et d’évaluer les mesures de sécurité utilisées pour protéger les …
The information and communication technologies are essential resources for organizations nowadays, and, with vast amounts of information circulating every day, protection becomes a priority. Various methodologies of information security risk analysis study and evaluate the security measures used to protect data. Traditional methods base their risk calculations on historical data, using threat- occurrence frequency as …
We all have questions, but who are the people with the answers for Cybersecurity. In this series we sat down with academics and experts to ask them about how they got started, what they are researching now, their lessons for us and the future. In this video, Holly An Garnett, Assistant Professor of Political Science …
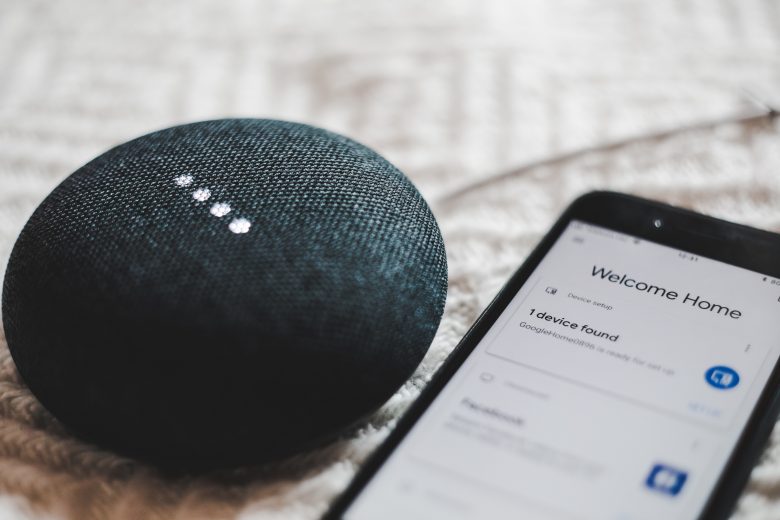
De nombreux appareils variés s’appuyant sur l’Internet des objets continuent de proliférer sur le marché. Les appareils domestiques intelligents aux multiples avantages sont commercialisés pour faciliter la vie des consommateurs et représentent par conséquent une part importante du marché de l’Internet des objet grand public. Les médias et les chercheurs ont soulevé des questions quant …
Numerous and various interconnected Internet of Things (IoT) devices continue to increase on the market. Smart home devices are marketed as providing multiple benefits to make consumers’ life more manageable and, as such, are a significant part of the loT consumer market. Media and researchers have raised questions about the security of smart home technology, …